
Cyber specialists from the “256th Cyber Assault Division,” together with the analytical group Ukrainian Militant and the international intelligence community InformNapalm, have accessed internal data from Russia’s Gonets satellite system.
According to InformNapalm, the operation lasted several years and resulted in the acquisition of internal documents from organizations supporting the Russian military.
The hackers reportedly gained access to private correspondence and official materials belonging to the deputy general director of JSC Satellite System Gonets and his subordinates.
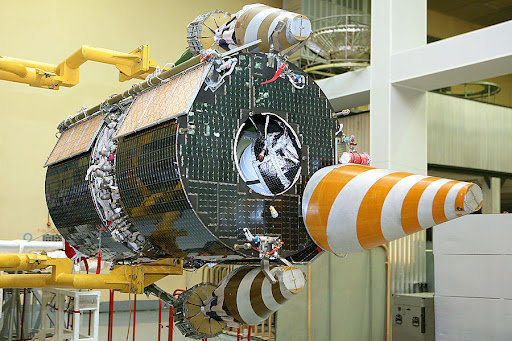
During 2023–2025, the obtained information was systematically passed to the Ukrainian Defense Forces. In Russia, the Gonets system is presented as a domestic analog of Starlink, with plans to eventually integrate its terminals into unmanned aerial vehicles.
However, in terms of technical specifications and capabilities, Gonets significantly lags behind the American system. The project represents a long-term effort to build a low-Earth-orbit communications network, but the quality of its services remains far below Starlink’s.
According to the leak, access was partly obtained through individuals within the company itself, including Deputy General Director Alexey Labzin. Vladimir Kataev, the chief specialist for cryptographic protection, handled information security.
The system’s ground infrastructure includes regional stations in Moscow, Zheleznogorsk, Yuzhno-Sakhalinsk, Murmansk, Rostov-on-Don, Norilsk, and Anadyr. Notably, a facility near the Orbita station in Anadyr is listed in documents using geographic coordinates instead of a standard address.
The leak also indicates that at the address 53/2 Baumanskaya Street, formally listed as the legal address, the system’s key IT infrastructure is actually concentrated. This is where the central software for control and access management is deployed, serving as the single hub for managing the entire network.
Among the obtained materials are data from the internal network and documentation related to the 1C platform, which is used to generate reports on the execution of state contracts within defense procurement for the Russian Ministry of Defense.
The documents also highlight the impact of international sanctions, particularly the use of outdated software.
Overall, the operation points not only to the compromise of a single enterprise but also to systemic cybersecurity weaknesses in Russia’s critical infrastructure.
The data suggests that even structures integrated into the military-industrial and space sectors remain vulnerable due to centralized architecture, outdated technologies, and human factors.
Previously, Ukrainian hackers had obtained information on the architecture of software tools used to develop and test systems for Russia’s strategic nuclear forces.


